Introduction
Web3 security has been a popular research field of information security in recent years. In this report, we collect, categorize, and briefly summarize 16 Web3-security-related papers from ACM CCS, NDSS, IEEE S&P, and USENIX Security conferences in 2023 and 2024, to identify common patterns and trends in this field. Note that I omit theoretical studies, which are out of my research scope.
The papers are categorized into four topics: vulnerability detection, novel attack & defense, optimization and privacy issues as shown in the following table. These topics provide a systemic view of Web3 security.
| Topic | Research |
|---|---|
| Vulnerability Detection |
Crush [1], VetEOS [3], SmartInv [4], Nyx [5], FuzzDelSol [6], Phoenix [8], ESCORT [10], LOKI [11], BlockScope [12], Panda [16] |
| Novel Attacks & Defenses |
Ma et al. [2], TxPhishScope [7], Sting [14], Ape [15] |
| Optimization | POSE [9] |
| Privacy Issues | Torres et al. [13] |
Topic 1: Vulnerability Detection
10 out of 16 collected studies aim to detect bugs or vulnerabilities in Web3 ecosystem.
VetEOS [3] is a static analysis tool for the Groundhog Day vulnerabilities in EOSIO contracts. In a Groundhog Day attack, attackers leverage the rollback issue in EOSIO contracts to persistently execute identical contract code with varying inputs. By using the information exposed in prior executions, attackers can accumulate insights about the target contract and figure out a reliable method to generate unauthorized profits. The authors formally define this vulnerability as a control and data dependency problem. The insight is that the vulnerability lies in intrinsic data and control dependencies among key contract constructs, such as user inputs, global states, database tables, API return values and inlined action calls. VetEOS performs context-sensitive flow-sensitive interprocedural dataflow analysis on EOSIO WebAssembly bytecode. Ultimately, VetEOS detected 735 new vulnerabilities in the wild.
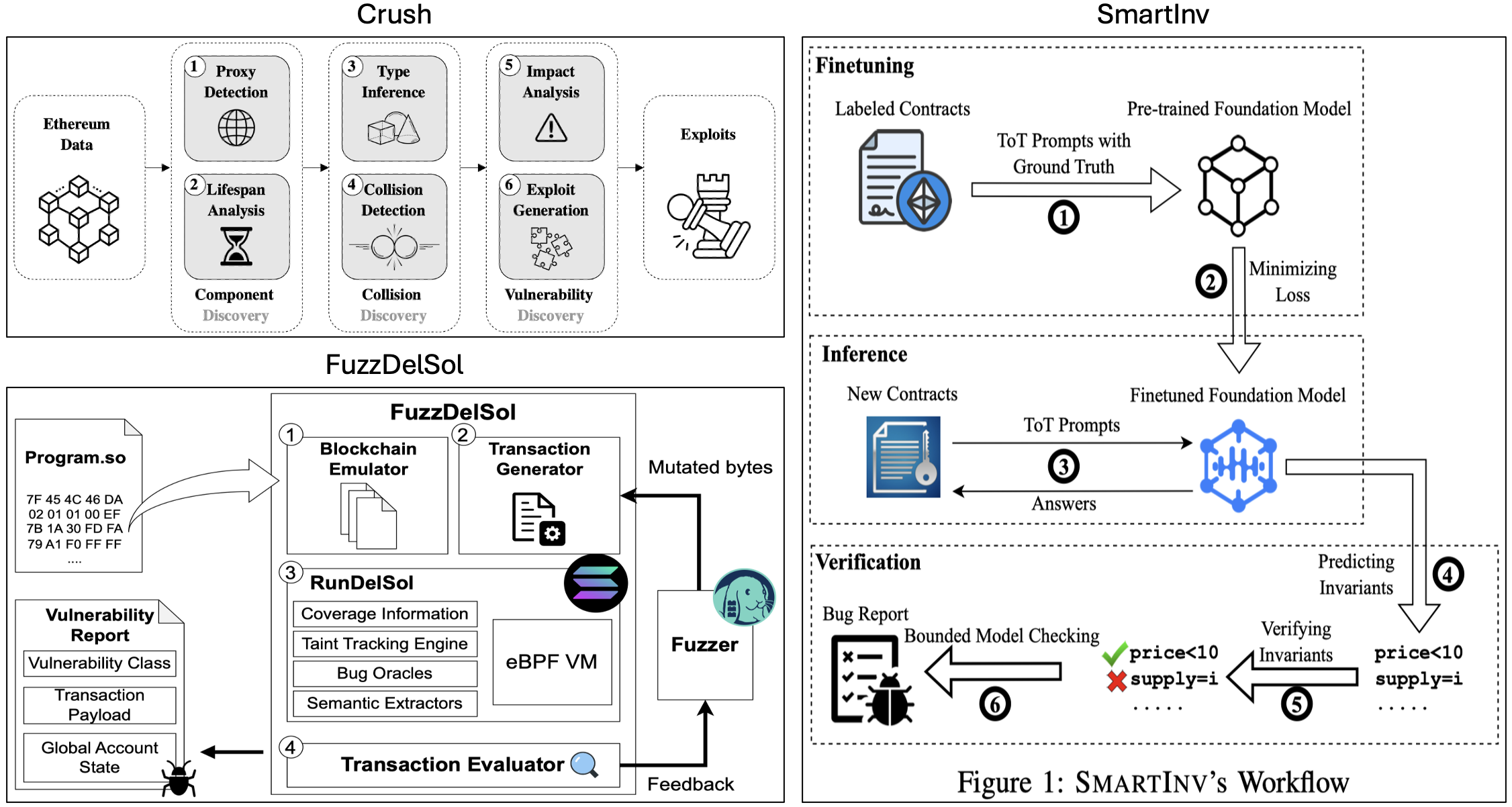
Crush [1] is an analysis system to detect and investigate a type of cross-contract vulnerability known as a storage collision at scale, which is resulted from the different understandings of the types/semantics of two contracts’ shared storage. Storage collision vulnerabilities may cause unexpected behavior such as denial of service (frozen funds), privilege escalation, and theft of financial assets. The approach is divided into three stages: component discovery, collision discovery, and vulnerability discovery, leveraging program analysis techniques. Crush performs a large-scale analysis of 14,237,696 smart contracts deployed on the Ethereum blockchain, identifies 14,891 potentially vulnerable contracts, and automatically synthesizes an end-to-end exploit for 956 of them.
SmartInv [4] is an accurate and fast smart contract invariant inference framework, which is used to detect machine un-auditable bugs. Such bugs cannot be reliably detected using existing automated tools that rely on pre-defined bug patterns. The insight is that the expected behavior of smart contracts, as specified by invariants, relies on understanding and reasoning across multimodal information, such as source code and natural language. The authors propose a new finetuning and prompting strategy to foundation models, Tier of Thought (ToT), to reason across multiple modalities of smart contracts and to generate invariants.
FuzzDelSol [6] is the first binary-only coverage-guided fuzzing architecture for Solana smart contracts. The authors extract low-level program and state information to develop a diverse set of bug oracles covering all major bug classes in Solana.
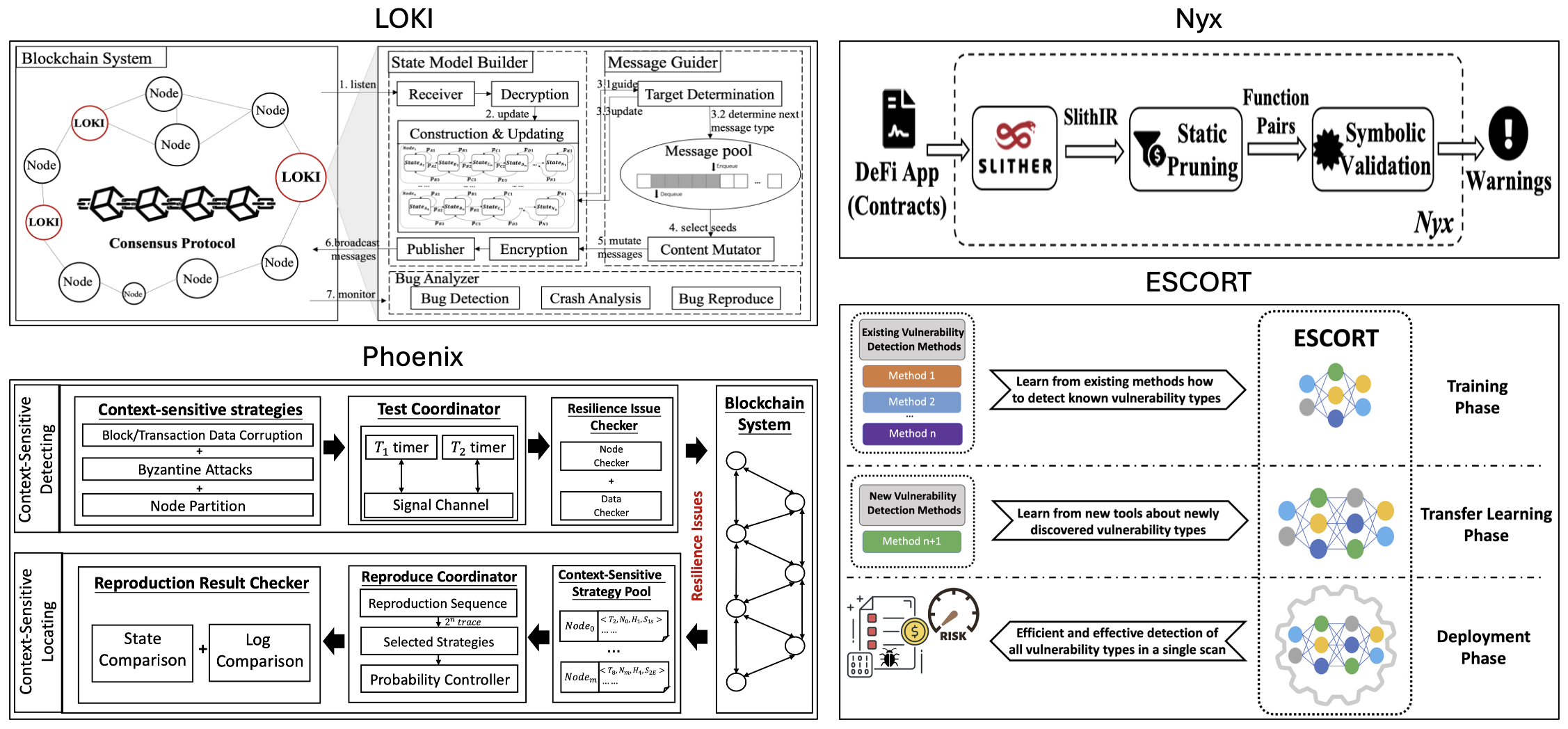
LOKI [11] is a blockchain consensus protocol fuzzing framework, which detects consensus memory-related and logic bugs. LOKI fetches consensus states in realtime by masquerading as a node. First, LOKI dynamically builds a state model that records the state transition of each node. After that, LOKI adaptively generates the input targets, types, and contents according to the state model. With a bug analyzer, LOKI detects the consensus protocol implementation bugs with well-defined oracles.
Nyx [5] is a static analyzer for detection of exploitable front-running vulnerabilities in smart contracts, which features a Datalog-based preprocessing procedure that efficiently and soundly prunes a large part of the search space, followed by a symbolic validation engine that precisely locates vulnerabilities with an SMT solver.
Phoenix [8] is a system for detecting and locating resilience issues in blockchain systems by context-sensitive chaos. The authors firstly identify two typical types of resilience issues in blockchain systems: node unrecoverable and data unrecoverable. Then, they design three context-sensitive chaos strategies tailored to the blockchain feature. They also create a coordinator to effectively trigger resilience issues by scheduling these strategies.
ESCORT [10] is a deep learning-based vulnerability detection method that uses a common feature extractor to learn generic bytecode semantics of smart contracts and separate branches to learn the features of each vulnerability type. As a multi-label classifier, ESCORT can detect multiple vulnerabilities of the contract at once. ESCORT is also the first deep learning-based framework utilizing transfer learning on new vunerability types with minimal model modification and retraining overhead.
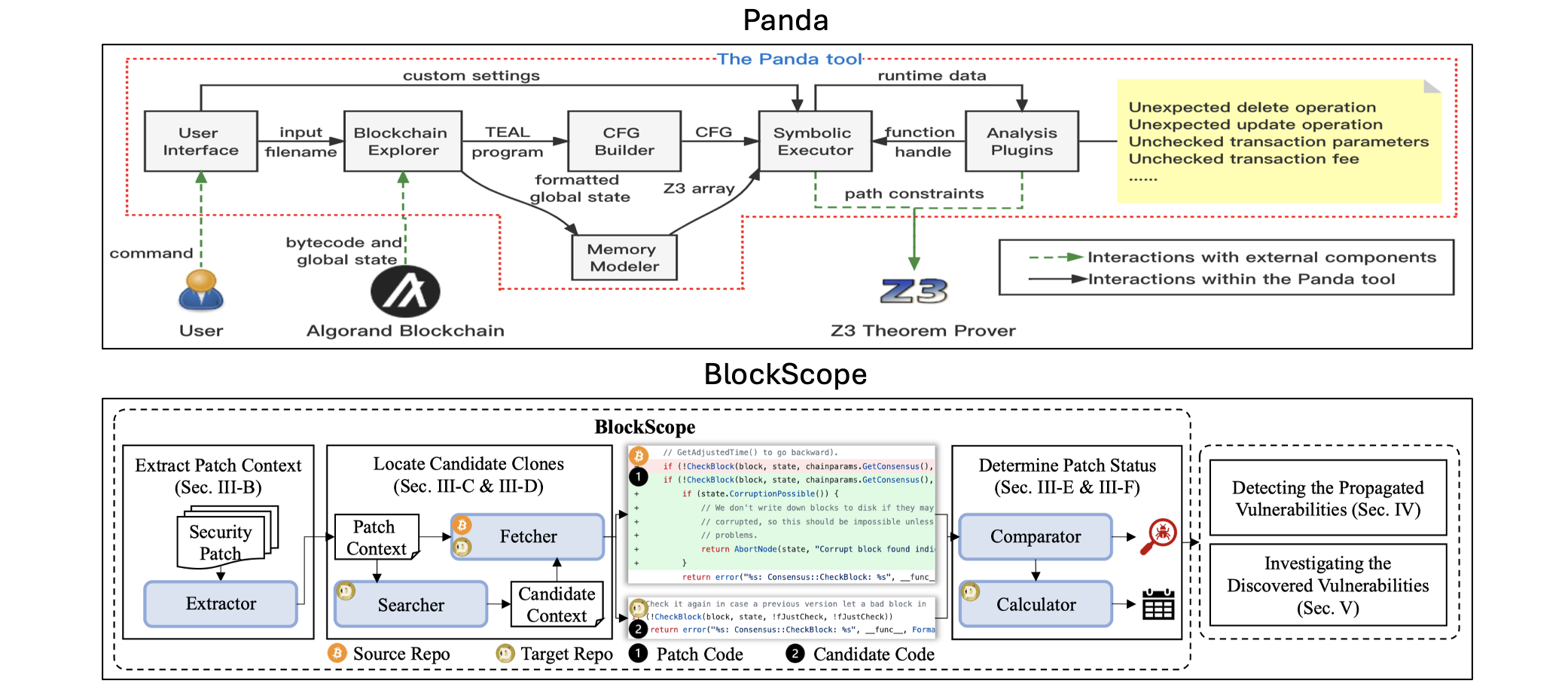
Panda [16] is the first extensible static analysis (symbolic execution and constraint solving) framework that automatically nine types of generic vulnerabilities in Algorand smart contracts. The authors also construct the first benchmark dataset to evaluate Panda.
BlockScope [12] is a patch-based code clone detection tool that can detect multiple types of cloned vulnerabilities given an input of existing Bitcoin/Ethereum security patches, leveraging similarity-based code match and proposing a new way of calculating code similarity to cover all the syntax-wide variant clones. To make BlockScope language-agnostic, there is no program analysis-alike preprocessing.
Topic 2: Novel Attacks & Defenses
In this section, we select four studies introducing novel attacks or defense mechanisms in Web3 security.
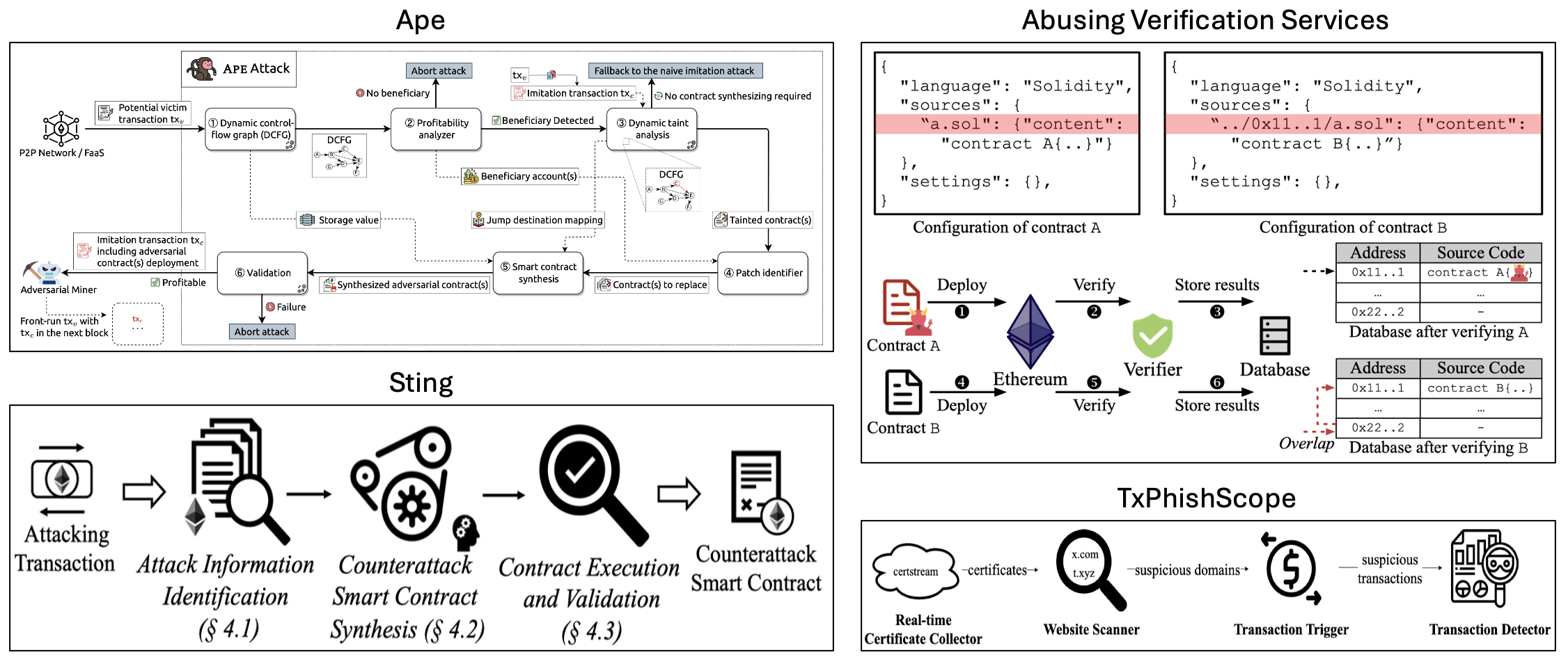
Ape [15] is a generalized imitation attack methodology. Imitation attack is one type of front-running attacks, where the attackers only copy-paste and front-run a pending profitable transaction without understanding its logic. Leveraging dynaic program analysis techniques (dynamic taint analysis, program synthesis, and advanced instrumentations), Ape supports the automatic synthesis of adversarial smart contracts. Besides attack, blockchain imitation can also act as an intrusion prevention system by mimicking an attack, appropriating the vulnerable funds, and returning them to its victim.
Ma et al. [2] presents the first comprehensive security analysis of smart contract verification services in the wild. By diving into the detailed workflow of existing verifiers, the authors summarized the key security properties that should be met, and observed eight types of vulnerabilities that can break the verification.
Sting [14] is a novel runtime defense mechanism against smart contract exploits. The key idea is to instantly synthesize counterattack smart contracts from attacking transactions and leverage the power of Maximal Extractable Value (MEV) to front run attackers.
TxPhishScope [7] is the largest TxPhish (transaction-based phishing scam) website detection system, which detects TxPhish websites and extracts phishing accounts automatically by dynamically visiting the suspicious websites, triggering transactions, and simulating results.
Topic 3: Optimization
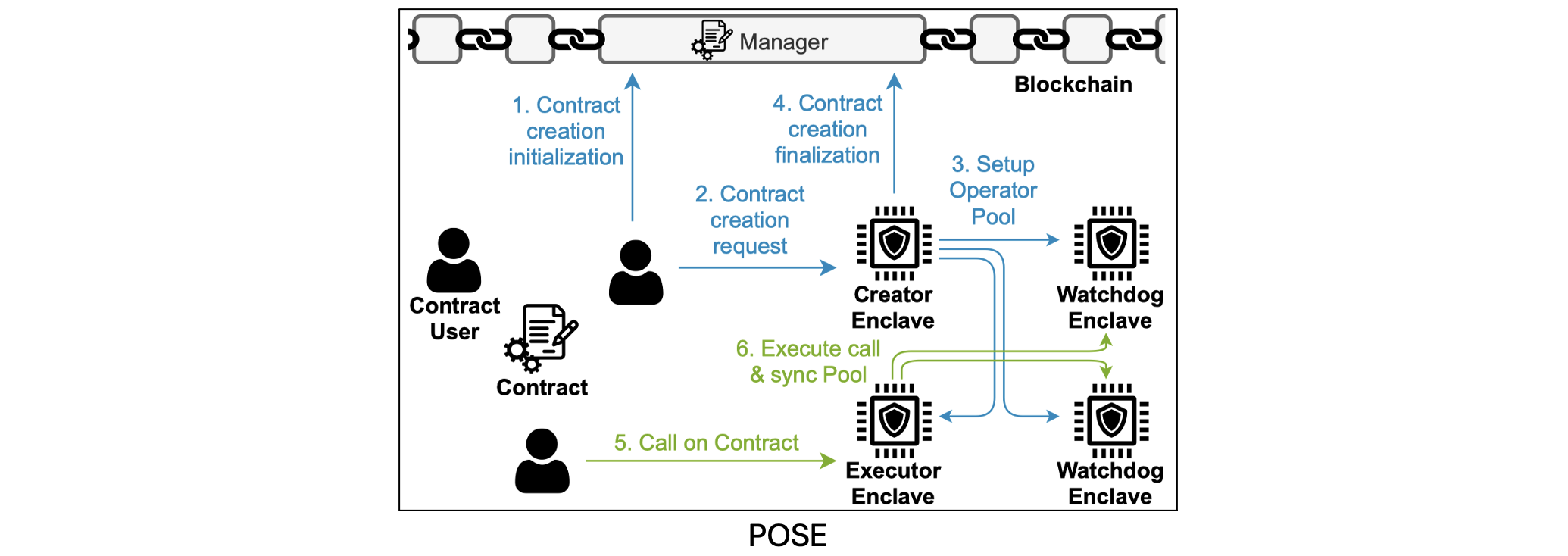
POSE [9] is a practical off-chain protocol for smart contracts that addresses shortcomings of existing off-chain solutions, such as costly blockchain interactions, lack of data privacy, huge capital costs from locked collateral, and supporting only a restricted set of applications. POSE leverages a pool of Trusted Execution Environments (TEEs) to execute the computation efficiently and to swiftly recover from accidental or malicious failures.
Topic 4: Privacy Issues
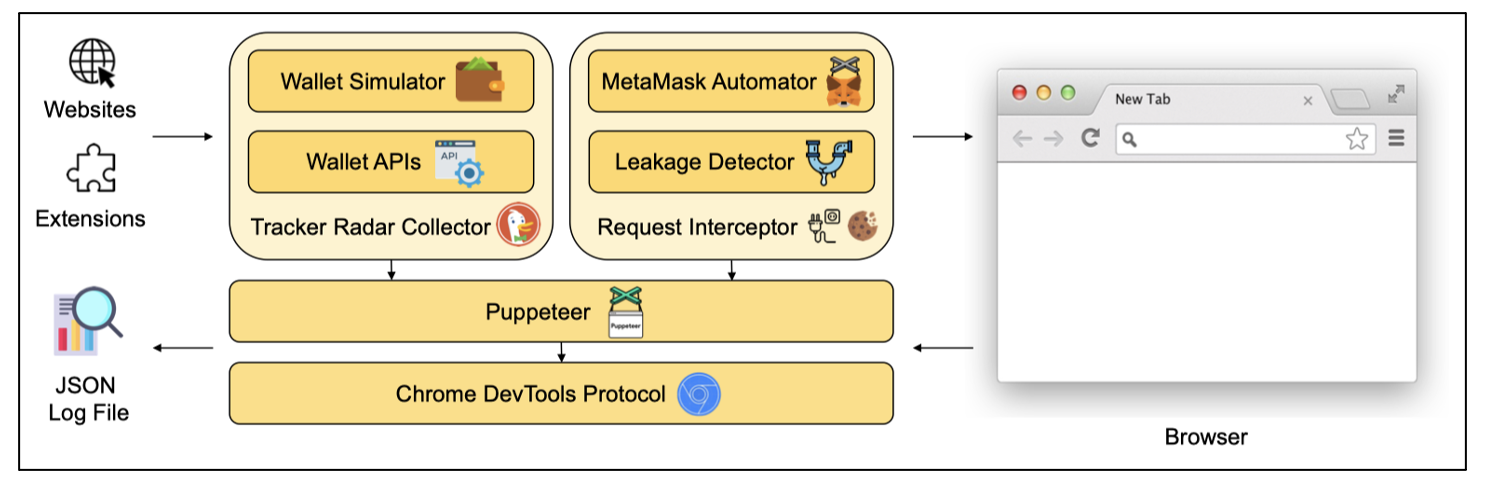
Torres et al. [13] analyzes the privacy implications that Web3 technologies have on users. The authors build a framework that measures exposure of wallet information. The evaluation results show that 1,325 from the top 100K websites run scripts to probe whether users have wallets installed in their browser, and there are more than 2000 leaks across 211 applications and over 300 leaks across 13 wallets, which leak the user’s unique wallet address to third-parties. The approach is tracking, intercepting and analyzing the network traffic.
References
NDSS'24
- [Crush] Ruaro, Nicola, et al. “Not your Type! Detecting Storage Collision Vulnerabilities in Ethereum Smart Contracts.”
- Ma, Pengxiang, et al. “Abusing the Ethereum Smart Contract Verification Services for Fun and Profit.” arXiv preprint arXiv:2307.00549 (2023).
- [vetEOS] Li, Levi Taiji, et al. “VETEOS: Statically Vetting EOSIO Contracts for the “Groundhog Day” Vulnerabilities.”
SP'24
- [SmartInv] Wang, Sally Junsong, Kexin Pei, and Junfeng Yang. “SMARTINV: Multimodal Learning for Smart Contract Invariant Inference.” 2024 IEEE Symposium on Security and Privacy (SP). IEEE Computer Society, 2024.
- [Nyx] Zhang, Wuqi, et al. “Nyx: Detecting Exploitable Front-Running Vulnerabilities in Smart Contracts.” 2024 IEEE Symposium on Security and Privacy (SP). IEEE Computer Society, 2024.
CCS'23
- [FuzzDelSol] Smolka, Sven, et al. “Fuzz on the Beach: Fuzzing Solana Smart Contracts.” Proceedings of the 2023 ACM SIGSAC Conference on Computer and Communications Security. 2023.
- [TxPhishScope] He, Bowen, et al. “TxPhishScope: Towards Detecting and Understanding Transaction-based Phishing on Ethereum.” Proceedings of the 2023 ACM SIGSAC Conference on Computer and Communications Security. 2023.
- [Phoenix] Ma, Fuchen, et al. “Phoenix: Detect and locate resilience issues in blockchain via context-sensitive chaos.” Proceedings of the 2023 ACM SIGSAC Conference on Computer and Communications Security. 2023.
NDSS'23
- [POSE] Frassetto, Tommaso, et al. “POSE: Practical off-chain smart contract execution.” arXiv preprint arXiv:2210.07110 (2022).
- [ESCORT] Sendner, Christoph, et al. “Smarter Contracts: Detecting Vulnerabilities in Smart Contracts with Deep Transfer Learning.” NDSS. 2023.
- [LOKI] Ma, Fuchen, et al. “LOKI: State-Aware Fuzzing Framework for the Implementation of Blockchain Consensus Protocols.” NDSS. 2023.
- [BlockScope] Yi, Xiao, et al. “BlockScope: Detecting and Investigating Propagated Vulnerabilities in Forked Blockchain Projects.” arXiv preprint arXiv:2208.00205 (2022).
Security'23
- Torres, Christof Ferreira, Fiona Willi, and Shweta Shinde. “Is your wallet snitching on you? an analysis on the privacy implications of web3.” 32nd USENIX Security Symposium (USENIX Security 23). 2023.
- [Sting] Zhang, Zhuo, et al. “Your exploit is mine: Instantly synthesizing counterattack smart contract.” 32nd USENIX Security Symposium (USENIX Security 23). 2023.
- [Ape] Qin, Kaihua, et al. “The blockchain imitation game.” 32nd USENIX Security Symposium (USENIX Security 23). 2023.
- [Panda] Sun, Zhiyuan, Xiapu Luo, and Yinqian Zhang. “Panda: Security analysis of algorand smart contracts.” 32nd USENIX Security Symposium (USENIX Security 23). 2023.